Yves here. A critical bit of context for this story: It’s a major departure for the defence and security writer for a major newspaper to have no experience in related fields, such as military, police or intelligence experience or war reporting.
By John Helmer, the longest continuously serving foreign correspondent in Russia, and the only western journalist to direct his own bureau independent of single national or commercial ties. Helmer has also been a professor of political science, and an advisor to government heads in Greece, the United States, and Asia. He is the first and only member of a US presidential administration (Jimmy Carter) to establish himself in Russia. Originally published at Dances with Bears
A fact which nobody can verify is usually a fiction, sometimes a lie. In the business of reporting news for sale, the demand for lies is less than the supply, so profit is bound to turn into loss. The only successful business models for reporting and repeating lies are government propaganda and commercial pornography.
Last July, when the Japanese Nikkei group paid £884 million for the Financial Times – saving Pearson Plc from reporting a loss for the financial year – Nikkei’s chief executive Tsuneo Kita said: “Our motto of providing high-quality reporting on economic and other news, while maintaining fairness and impartiality, is very close to that of the FT. We share the same journalistic values. Together, we will strive to contribute to the development of the global economy.” If Kita was asked how much money he would spend on Sam Jones to sell lies about Russia three times a week, he would do more than ask: “Sam Who?”
There are 558,000 people named Jones in the UK; 1.6 million in the US. Altogether, 2.2 million. Among the Sam Joneses, of whom there are more than a thousand, the majority would never think of repeating, unverified, every word passed in a classified file from US intelligence, British MI6 and NATO. There is just one Sam Jones in the world who does that. At the Financial Times office in London, he is called “defence and security editor”.
In Boolean searches on the internet, the AND operator returns a value of TRUE if both its operands are TRUE, and FALSE otherwise. If you are paying Nikkei for the Jones defence and security stories each week, you are getting double the falsehood for your money.
On February 19, Jones reported a story which was headlined “Russia steps up Syria cyber assault”. The full text can be read here. The news appears to be that what is reported in western media from Syrian sources about the war in Syria has been fabricated by a special department of the Kremlin’s security agencies. This is being accomplished by a form of electronic espionage which penetrates Syrian human rights organizations, fighters on the ground, Syrian refugees, not to mention Turks, and puts words in their mouths which they didn’t say; and which have been put there by their Russian adversaries. “Russia is deliberately weaponising the Syrian refugee crisis,” Jones reports, “by attacking civilian targets in the country to increase pressure on Europe”. Pushing Syrians and Turks into flooding across Europe’s borders, where they aren’t wanted, is reported to be a Russian military tactic.
This may be true. For his evidence Jones cites “two senior intelligence officials, one from Europe and one from a country on the Styrian border.” The British intelligence officer doesn’t tell Jones much. The Turkish officer is reported as “speaking on condition of anonymity… that the campaign was directed by the FSB, Russia’s state security agency.” According to Jones, “ ‘there’s a major Russian cyber response right now because of a worsening relationship [with Ankara],’ the regional intelligence official said, citing Turkey’s shooting down of a Russian jet in November as a turning point.”
This is evidence there is a shooting war going on, but that’s not news. So the British agent is cited by Jones for the “fear that that could allow Russia to mount a significant disinformation campaign if it chooses too [sic], greatly complicating the situation.” The Russian disinformation, according to the Jones sources, is to discredit “the most important human rights organisations and aid groups operating in the country, such as the Syrian Observatory of Human Rights, which reports on military incidents and is frequently cited in western media outlets.”
How and what to believe on a war front threatening Europe and the rest of the world would be part of the Nikkei business model if it does defence and security editing like reporter Jones and chief executive Kita. So apart from a Turk speaking anonymously what evidence do they present the paying readers?
A US-based, Nasdaq-listed company selling information technology services is cited as their source. According to the Financial Times, “Richard Turner, head of Middle East and Europe at FireEye, the cyber security group, said that his organisation had tracked Moscow’s cyber campaign against Syrian organisations since December, adding that it had been growing in size since the start of the year.”
The Russian campaign, according to FireEye, is intelligence-gathering – to find out what the enemy is thinking and doing. It is also a deception operation to get the enemy and its allies to make mistakes on the battlefield. For more on the history of these aspects of conventional warfare, read this. FireEye is quoted by Jones as saying something more concrete: “The Syrian cyber attacks are mounted using fake replicas of legitimate organisations’ websites, which infect computer users when they are accessed. They also involve crafting cleverly disguised emails with malign attachments designed to look like trusted personal correspondences, press releases or official notices. ‘It could be for two reasons,’ said Jens Monrad, global intelligence liaison at FireEye. ‘One is to send out false information from those groups, or groups, or they could be using their credentials as stepping stones to go on and target other individuals or organisations. It all fits with Russia’s traditional information warfare doctrine.’ ”
FireEye is based in California, with a government client office in Reston, Virginia. Turner (below left) and Monrad (right) are based at the FireEye office in London.

Turner’s business resume is a string of computer technology and data security companies called Clearwswift, Proofpoint, and now FireEye. Companies spying on each other and phishing-type data and credit card fraud have been his specialities. But the stockmarket records for Proofpoint and FireEye are showing that sales for this type of product peaked last year; revenues, profits, and share prices have been plummeting since then. Turner is a salesman for finding new buyers for information security services. “Most organizations spend on low-value business problems and legacy security,” Turner told a security industry newsletter. “It should be a shareholder value issue. A data breach affects profitability. Re-prioritising spend would absolutely benefit most organizations. It’s important to understand that the adversary has changed and the strategy to combat has moved on.”
Monrad, a Danish systems engineer, reports that for most of his career he worked in secret as a “trusted security advisor for undisclosed organizations and companies.” He’s been working in the open for less than two years, first for a Danish group called IT-Branchen in Copenhagen, then for a European Commission unit called ENISA – European Union Agency for Network and Information Security. The intelligence liaison job Monrad was hired a few months ago to do at FireEye is liaison with the intelligence agencies Monrad used to work for.
Turner and Monrad told Jones for publication in the Financial Times last week that “APT 28 and other Russian groups are now really focusing their attention on the collection of data on Syrian groups, particularly those focused on human rights and the monitoring of Russian military activity…It’s a very significant operation.” APT 28, according to them and to the Financial Times, “is one of Russia’s most highly sophisticated cadres of state-backed hackers.”
This may be true. By telephone and email Turner and Monrad were asked “for examples of the materials you are referring to, and for your evidence for identifying the source, according to the FT report, as directed by the FSB, Russia’s state security agency.” They responded through a company spokesman with “three reports that we have about Russian cyber actors that shows our thought process on what we have seen.”

One of the reports was issued in 2014; the other two appeared in June 2015 and November 2015. One report mentions “an advanced persistent threat group that we suspect the Russian government sponsors”; another, “suspected nation-state sponsored cyber actors engaged in a large-scale reconnaissance effort.” There is no mention of the war in Syria or of Russian operations in Syria.
Turner and Monrad were asked again to provide examples of the evidence they gave the Financial Times – “fake replicas”, “disguised emails”, “malign attachments” – and of evidence of their Russian origin at the FSB. They replied: “Based on the technical indicators, we believe there is a significant overlap of infrastructure, tactics, techniques and procedures being used by what we suspect to be a threat actor based in Russia. At this stage we cannot provide extended details on these at the current time. We can discuss how we attribute cyber operations in our previous reports in a few weeks. Also, when private security companies attribute operations, we are often unable to determine the exact organization or individuals behind it. We leave it to the intelligence professionals in government to take that next step.”
In one of last year’s reports, Turner , Monrad and their colleagues reported: “Our clients often ask us to assess the threat Russia poses in cyberspace.” Last Friday they were asked to clarify: “Are government agencies among the clients to which this line refers? So as not to impinge on your client confidentiality, a yes or no will suffice.” They refused to say.
The Financial Times reports that Jones was hired in 2007 as a reporter on hedge funds and financial markets. He had worked for Euromoney before that. For education the newspaper says he graduated from the London School of Economics with a history degree. A content analysis of his FT reporting found that that ISIS, Russia, and NATO were the topics he mentions most often.
Jones also publishes a Twitter column with a sub-specialization on homophobia in Russia. The Twitter network promoting this material can be tracked here.
The FireEye disclaimers were reported to Jones. “FireEye is unable to provide the evidence you cite. May I ask you to provide the evidence on which you have relied for your claims?” He did not reply.
Pearson Plc, which until recently owned the Financial Times, is an American business with a London exchange listing. Until the Financial Times was sold to the Japanese last year, the newspaper was worth only 10% of the group’s dwindling revenue stream. It will be double that share in the Nikkei group’s $1.5 billion annual revenue, also dwindling.
The latest Pearson financial report confirms that without the disposal of the FT, the group’s bottom-line would have been negative.
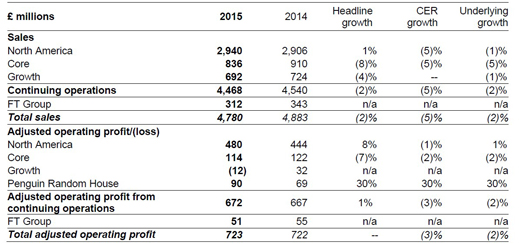
The Pearson financial report goes on: “Discontinued operations in 2015 relate to the sale of the Financial Times and the Group’s 50% interest in the Economist. The Economist sale was substantially completed on 16 October 2015 and realised a gain of £473m before tax. The sale of the Financial Times completed on 30 November 2015 and realised a gain of £711m before tax. We expect both of these transactions to qualify for substantial shareholder exemption in the UK. The gains on these transactions and the results for both 2014 and 2015 to the respective sale dates have been included in discontinued operations.”
Nikkei Inc. isn’t a publicly listed company; its shareholders are its employees. But as the stock market understands the value of Pearson Plc, the future was deteroriating before the sale of the newspaper; it then got 68% worse than it had been.
ONE-YEAR SHARE PRICE TRAJECTORY FOR PEARSON PLC

Source: http://www.bloomberg.com/quote/PSON:LN
In the US stock market FireEye is deteriorating even faster.
ONE-YEAR SHARE PRICE TRAJECTORY FOR FIREEYE

Source: http://www.bloomberg.com/quote/FEYE:US
The reason is that despite growth of revenue from acquiring new product and service companies and adding to aggregate billings, FireEye is lossmaking, and expects to continue to lose money this year. For the financial details released earlier this month, read this report. The company presentations do not explain why the losses are mounting except that the costs of doing and advertising its business are rising faster than the fees clients are willing to pay.
 Directed by Kevin Mandia (right), a former US Air Force investigator and Pentagon security officer, FireEye is desperate to identify new cyber threats and market its services to combat them to new clients. “In 2015,” Mandia said last week, “we continued to be reminded that there is no such thing as perfect security. Based on the significant number of incidents that Mandiant [FireEye subsidiary] investigated in 2015, threat actors are finding inventive and disruptive ways to skirt even the best defenses, resulting in informational, financial and reputational loss.”
Directed by Kevin Mandia (right), a former US Air Force investigator and Pentagon security officer, FireEye is desperate to identify new cyber threats and market its services to combat them to new clients. “In 2015,” Mandia said last week, “we continued to be reminded that there is no such thing as perfect security. Based on the significant number of incidents that Mandiant [FireEye subsidiary] investigated in 2015, threat actors are finding inventive and disruptive ways to skirt even the best defenses, resulting in informational, financial and reputational loss.”
When Jones reports FireEye’s detection of Russian threats in the Financial Times, he is advertising FireEye’s services. When the FireEye analysts and Jones can’t substantiate the threat claims, they are advertising something else. Jones was asked: “In relation to FireEye, will you say whether you have received any form of entertainment, hospitality, trip, accommodation or benefit from FireEye or its associated interests?” Jones is refusing to answer.


Yves,
In my view, you have really stepped up your game in terms of aggregative, geopolitical reporting in recent months. This makes your site increasingly important for those seeking real reporting in a media world that is otherwise polluted with propaganda and bias.
Though small potatoes, I’m going to contribute again in a further show of appreciation.
Cheers,
Tink
Wow. Those dots almost connect themselves. No doubt Mr. Jones can look forward to a scintillating career trajectory akin to Judy Miller’s. He just needs something really meaty to latch onto. Like the security remoras from FireEye and Mandiant who are also desperately seeking a .gov host.
I was much amused by this: The Russian disinformation, according to the Jones sources, is to discredit “the most important human rights organisations and aid groups operating in the country, such as the Syrian Observatory of Human Rights, which reports on military incidents and is frequently cited in western media outlets.” I nearly squirted coffee out of my nose! As if anyone needs to discredit SOHR; he does such a great job himself from his dress shoppe that he really doesn’t need any help.
I’ll bet his services were bought cheap too. Or not even bought – he may be a fellow-traveller working his own agenda.
Propagandists are such marginal people!
The truth is hardly ever what it appears to be…nice piece on smoke and mirrors reporting feeding the needs of a qouted party…
Reading financial news like one might have needed to read pravda back in a previous generation…
who is saying what and why and what are they trying to sell us…
Thanks for another John Helmer column. I find him to be THE best source for politically juicy economic shenanigans, not only of Russian oligarchs, but of related western news matters as well. I wish there were a journalist writing regular columns with this depth of coverage in the Atlanticist media. First rate.
I worked in the IT industry in Denmark for many years. The Danish group IT-Branchen that Monrad says he works for/with in Copenhagen is basically a lobbyist group for the established players of the Danish IT world, including all the usual suspects, the big retailers, and others. This group has more or less no international interests or contacts of any kind, except perhaps to supplier countries like the USA or China. They are mainly put in the world to organise meaningless forums and symposiums about leadership and virtual reality and to pontificate on things that might affect the bottom line of their members.
The thought that they might be involved in any meaningful activities involved with international security, especially in the Middle East, is absurd. At most Monrad would be talking to them about hackers threatening Danish companies.
Monrad, funnily enough, is also the name of a really puerile Danish comedian. I am not suggesting there is any connection, of course.
Thanks for posting this, Yves. While I’m sure the Russians are engaged in surveillance and what might be characterized as cyberwarfare in pursuit of a favorable outcome in Syria, to build on that to claim that they are deliberately creating a refugee problem strikes me as ridiculous, particularly after Erdogan’s recent “weaponizing” of refugees in his sparring with the EU.