Yves here. The first release of the Wikileaks Vault 7 trove has curiously gone from being a MSM lead story yesterday to a handwave today. On the one hand, anyone who was half awake during the Edward Snowden revelations knows that the NSA is in full spectrum surveillance and data storage mode, and members of the Five Eyes back-scratch each other to evade pesky domestic curbs on snooping. So the idea that the CIA (and presumably the NSA) found a way to circumvent encryption tools on smartphones, or are trying to figure out how to control cars remotely, should hardly come as a surprise.
However, at a minimum, reminding the generally complacent public that they are being spied on any time they use the Web, and increasingly the times in between, makes the officialdom Not Happy.
And if this Wikileaks claim is even halfway true, its Vault 7 publication is a big deal:
Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
This is an indictment of the model of having the intelligence services rely heavily on outside contractors. It is far more difficult to control information when you have multiple organizations involved. In addition, neolibearlism posits that workers are free agents who have no loyalties save to their own bottom lines (or for oddballs, their own sense of ethics). Let us not forget that Snowden planned his career job moves, which included a stint at NSA contractor Dell, before executing his information haul at a Booz Allen site that he had targeted.
Admittedly, there are no doubt many individuals who are very dedicated to the agencies for which they work and aspire to spend most it not all of their woking lives there. But I would assume that they are a minority.
The reason outsiders can attempt to pooh-pooh the Wikileaks release is that the organization redacted sensitive information like the names of targets and attack machines. The CIA staffers who have access to the full versions of these documents as well as other major components in the hacking toolkit will be the ones who can judge how large and serious the breach really is.1 And their incentives are to minimize it no matter what.
By Gaius Publius, a professional writer living on the West Coast of the United States and frequent contributor to DownWithTyranny, digby, Truthout, and Naked Capitalism. Follow him on Twitter @Gaius_Publius, Tumblr and Facebook. GP article archive here. Originally published at DownWithTyranny
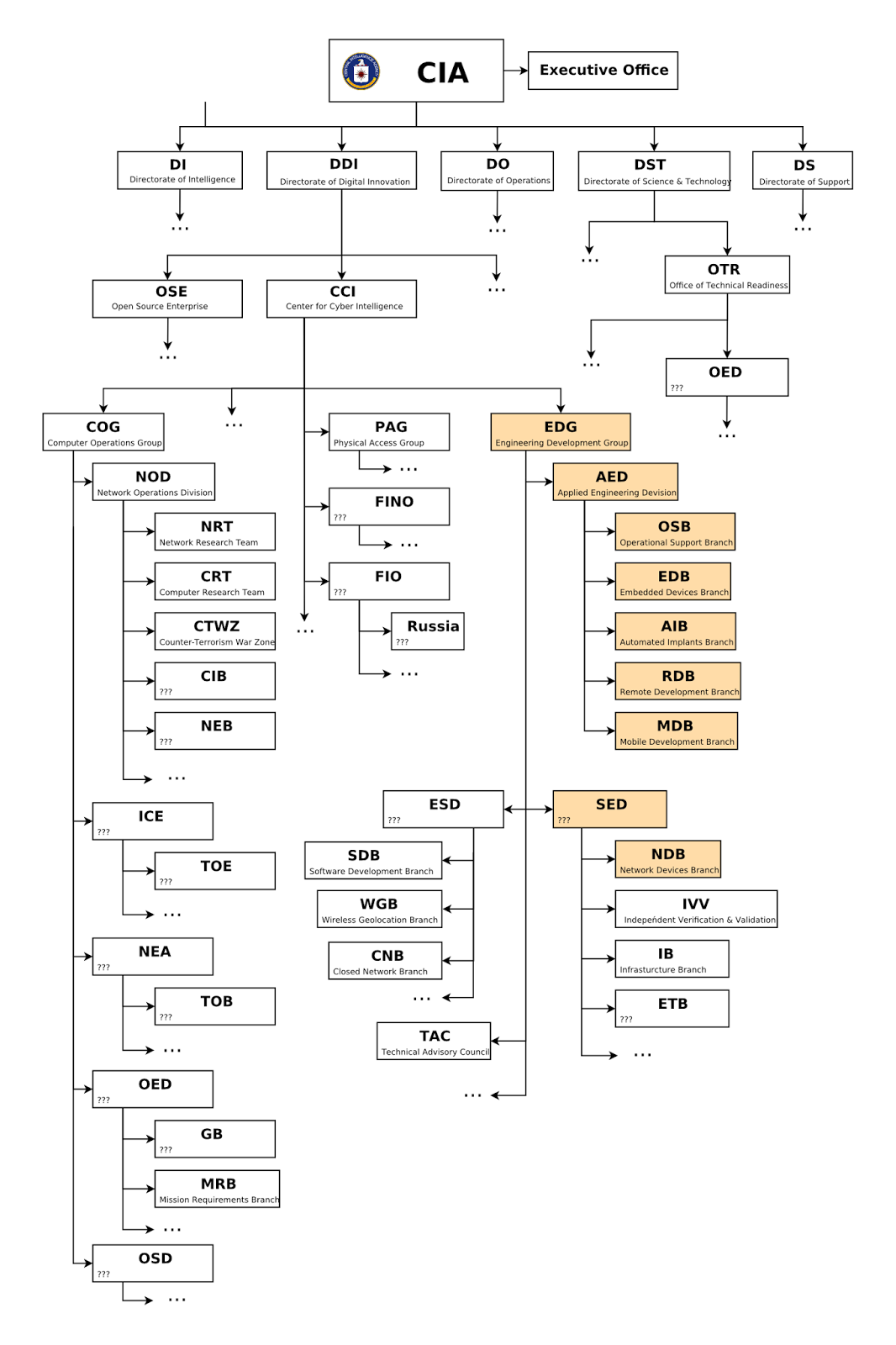
CIA org chart from the WikiLeaks cache (click to enlarge). “The organizational chart corresponds to the material published by WikiLeaks so far. Since the organizational structure of the CIA below the level of Directorates is not public, the placement of the EDG [Engineering Development Group]and its branches … is reconstructed from information contained in the documents released so far. It is intended to be used as a rough outline of the internal organization; please be aware that the reconstructed org chart is incomplete and that internal reorganizations occur frequently.”
Bottom line first. As you read what’s below, consider:
- That the CIA is capable of doing all of the things described, and has been for years, is not in doubt.
- That unnameable many others have stolen (“exfiltrated”) these tools and capabilities is, according to the Wikileaks leaker, also certain. Consider this an especially dangerous form of proliferation, with cyber warfare tools in the hands of anyyone with money and intent. As WikiLeaks notes, “Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by peer states, cyber mafia and teenage hackers alike.”
- That the CIA is itself using these tools, and if so, to what degree, are the only unknowns. But can anyone doubt, in this aggressively militarized environment, that only the degree of use is in question?
Now the story.
WikiLeaks just dropped a huge cache of documents (the first of several promised releases), leaked from a person or people associated with the CIA in one or more capacities (examples, employee, contractor), which shows an agency out-of-control in its spying and hacking overreach. Read through to the end. If you’re like me, you’ll be stunned, not just about what they can do, but that they would want to do it, in some cases in direct violation of President Obama’s orders. This story is bigger than anything you can imagine.
Consider this piece just an introduction, to make sure the story stays on your radar as it unfolds — and to help you identify those media figures who will try to minimize or bury it. (Unless I missed it, on MSNBC last night, for example, the first mention of this story was not Chris Hayes, not Maddow, but the Lawrence O’Donnell show, and then only to support his guest’s “Russia gave us Trump” narrative. If anything, this leak suggests a much muddier picture, which I’ll explore in a later piece.)
So I’ll start with just a taste, a few of its many revelations, to give you, without too much time spent, the scope of the problem. Then I’ll add some longer bullet-point detail, to indicate just how much of American life this revelation touches.
While the cache of documents has been vetted and redacted, it hasn’t been fully explored for implications. I’ll follow this story as bits and piece are added from the crowd sourced research done on the cache of information. If you wish to play along at home, the WikiLeaks torrent file is here. The torrent’s passphrase is here. WikiLeaks press release is here (also reproduced below). Their FAQ is here.
Note that this release covers the years 2013–2016. As WikiLeaks says in its FAQ, “The series is the largest intelligence publication in history.”
Preface — Trump and Our “Brave New World”
But first, this preface, consisting of one idea only. Donald Trump is deep in the world of spooks now, the world of spies, agents and operatives. He and his inner circle have a nest of friends, but an even larger, more varied nest of enemies. As John Sevigny writes below, his enemies include not only the intel and counter-intel people, but also “Republican lawmakers, journalists, the Clintons, the Bush family, Barack Obama, the ACLU, every living Democrat and even Rand Paul.” Plus Vladimir Putin, whose relationship with Trump is just “business,” an alliance of convenience, if you will.
I have zero sympathy for Donald Trump. But his world is now our world, and with both of his feet firmly planted in spook world, ours are too. He’s in it to his neck, in fact, and what happens in that world will affect every one of us. He’s so impossibly erratic, so impossibly unfit for his office, that everyone on the list above wants to remove him. Many of them are allied, but if they are, it’s also only for convenience.
How do spooks remove the inconvenient and unfit? I leave that to your imagination;they have their ways. Whatever method they choose, however, it must be one without fingerprints — or more accurately, without their fingerprints — on it.
Which suggests two more questions. One, who will help them do it, take him down? Clearly, anyone and everyone on the list. Second, how do you bring down the president, using extra-electoral, extra-constitutional means, without bringing down the Republic? I have no answer for that.
Here’s a brief look at “spook world” (my phrase, not the author’s) from “The Fox Hunt” by John Sevigny:
Several times in my life – as a journalist and rambling, independent photographer — I’ve ended up rubbing shoulders with spooks. Long before that was a racist term, it was a catch-all to describe intelligence community people, counter intel types, and everyone working for or against them. I don’t have any special insight into the current situation with Donald Trump and his battle with the IC as the intelligence community calls itself, but I can offer a few first hand observations about the labyrinth of shadows, light, reflections, paranoia, perceptions and misperceptions through which he finds himself wandering, blindly. More baffling and scary is the thought he may have no idea his ankles are already bound together in a cluster of quadruple gordian knots, the likes of which very few people ever escape.
Criminal underworlds, of which the Trump administration is just one, are terrifying and confusing places. They become far more complicated once they’ve been penetrated by authorities and faux-authorities who often represent competing interests, but are nearly always in it for themselves.
One big complication — and I’ve written about this before — is that you never know who’s working for whom. Another problem is that the heirarchy of handlers, informants, assets and sources is never defined. People who believe, for example, they are CIA assets are really just being used by people who are perhaps not in the CIA at all but depend on controlling the dupe in question. It is very simple — and I have seen this happen — for the subject of an international investigation to claim that he is part of that operation. [emphasis added]
Which leads Sevigny to this observation about Trump, which I partially quoted above: “Donald Trump may be crazy, stupid, evil or all three but he knows the knives are being sharpened and there are now too many blades for him to count. The intel people are against him, as are the counter intel people. … His phone conversations were almost certainly recorded by one organization or another, legal or quasi legal. His enemies include Republican lawmakers, journalists, the Clintons, the Bush family, Barack Obama, the ACLU, every living Democrat and even Rand Paul. Putin is not on his side — that’s a business matter and not an alliance.”
Again, this is not to defend Trump, or even to generate sympathy for him — I personally have none. It’s to characterize where he is, and we are, at in this pivotal moment. Pivotal not for what they’re doing, the broad intelligence community. But pivotal for what we’re finding out, the extent and blatancy of the violations.
All of this creates an incredibly complex story, with only a tenth or less being covered by anything like the mainstream press. For example, the Trump-Putin tale is much more likely to be part of a much broader “international mobster” story, whose participants include not only Trump and Putin, but Wall Street (think HSBC) and major international banks, sovereign wealth funds, major hedge funds, venture capital (vulture capital) firms, international drug and other trafficking cartels, corrupt dictators and presidents around the world … and much of the highest reaches of the “Davos crowd.”
Much of the highest reaches of the .01 percent, in other words, all served, supported and “curated” by the various, often competing elements of the first-world military and intelligence communities. What a stew of competing and aligned interests, of marriages and divorces of convenience, all for the common currencies of money and power, all of them dealing in death.
What this new WikiLeaks revelation shows us is what just one arm of that community, the CIA, has been up to. Again, the breadth of the spying and hacking capability is beyond imagination. This is where we’ve come to as a nation.
What the CIA Is Up To — A Brief Sample
Now about those CIA spooks and their surprising capabilities. A number of other outlets have written up the story, but this from Zero Hedge has managed to capture the essence as well as the breadth in not too many words (emphasis mine throughout):
WikiLeaks has published what it claims is the largest ever release of confidential documents on the CIA. It includes more than 8,000 documents as part of ‘Vault 7’, a series of leaks on the agency, which have allegedly emerged from the CIA’s Center For Cyber Intelligence in Langley, and which can be seen on the org chart below, which Wikileaks also released: [org chart reproduced above]
A total of 8,761 documents have been published as part of ‘Year Zero’, the first in a series of leaks the whistleblower organization has dubbed ‘Vault 7.’ WikiLeaks said that ‘Year Zero’ revealed details of the CIA’s “global covert hacking program,” including “weaponized exploits” used against company products including “Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.”
WikiLeaks tweeted the leak, which it claims came from a network inside the CIA’s Center for Cyber Intelligence in Langley, Virginia.
Among the more notable disclosures which, if confirmed, “would rock the technology world“, the CIA had managed to bypass encryption on popular phone and messaging services such as Signal, WhatsApp and Telegram. According to the statement from WikiLeaks, government hackers can penetrate Android phonesand collect “audio and message traffic before encryption is applied.”
With respect to hacked devices like you smart phone, smart TV and computer, consider the concept of putting these devices in “fake-off” mode:
Among the various techniques profiled by WikiLeaks is “Weeping Angel”, developed by the CIA’s Embedded Devices Branch (EDB), which infests smart TVs, transforming them into covert microphones. After infestation, Weeping Angel places the target TV in a ‘Fake-Off’ mode, so that the owner falsely believes the TV is off when it is on. In ‘Fake-Off’ mode the TV operates as a bug, recording conversations in the room and sending them over the Internet to a covert CIA server.
As Kim Dotcom chimed in on Twitter, “CIA turns Smart TVs, iPhones, gaming consoles and many other consumer gadgets into open microphones” and added “CIA turned every Microsoft Windows PC in the world into spyware. Can activate backdoors on demand, including via Windows update“[.]
Do you still trust Windows Update?
About “Russia did it”…
Adding to the “Russia did it” story, note this:
Another profound revelation is that the CIA can engage in “false flag” cyberattacks which portray Russia as the assailant. Discussing the CIA’s Remote Devices Branch’s UMBRAGE group, Wikileaks’ source notes that it “collects and maintains a substantial library of attack techniques ‘stolen’ from malware produced in other states including the Russian Federation.[“]
As Kim Dotcom summarizes this finding, “CIA uses techniques to make cyber attacks look like they originated from enemy state….”
This doesn’t prove that Russia didn’t do it (“it” meaning actually hacking the presidency for Trump, as opposed to providing much influence in that direction), but again, we’re in spook world, with all the phrase implies. The CIA can clearly put anyone’s fingerprints on any weapon they wish, and I can’t imagine they’re alone in that capability.
Hacking Presidential Devices?
If I were a president, I’d be concerned about this, from the WikiLeaks “Analysis” portion of the Press Release (emphasis added):
“Year Zero” documents show that the CIA breached the Obama administration’s commitments [that the intelligence community would reveal to device manufacturers whatever vulnerabilities it discovered]. Many of the vulnerabilities used in the CIA’s cyber arsenal are pervasive [across devices and device types] and some may already have been found by rival intelligence agencies or cyber criminals.
As an example, specific CIA malware revealed in “Year Zero” [that it] is able to penetrate, infest and control both the Android phone and iPhone software that runs or has run presidential Twitter accounts. The CIA attacks this software by using undisclosed security vulnerabilities (“zero days”) possessed by the CIA[,] but if the CIA can hack these phones then so can everyone else who has obtained or discovered the vulnerability. As long as the CIA keeps these vulnerabilities concealed from Apple and Google (who make the phones) they will not be fixed, and the phones will remain hackable.
Does or did the CIA do this (hack presidential devices), or is it just capable of it? The second paragraph implies the latter. That’s a discussion for another day, but I can say now that both Lawrence Wilkerson, aide to Colin Powell and a non-partisan (though an admitted Republican) expert in these matters, and William Binney,one of the triumvirate of major pre-Snowden leakers, think emphatically yes. (See Wilkerson’s comments here. See Binney’s comments here.)
Whether or not you believe Wilkerson and Binney, do you doubt that if our intelligence people can do something, they would balk at the deed itself, in this world of “collect it all“? If nothing else, imagine the power this kind of bugging would confer on those who do it.
The Breadth of the CIA Cyber-Hacking Scheme
But there is so much more in this Wikileaks release than suggested by the brief summary above. Here’s a bullet-point overview of what we’ve learned so far, again via Zero Hedge:
Key Highlights from the Vault 7 release so far:
- “Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
- Wikileaks claims that the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
- By the end of 2016, the CIA’s hacking division, which formally falls under the agency’s Center for Cyber Intelligence (CCI), had over 5000 registered users and had produced more than a thousand hacking systems, trojans, viruses, and other “weaponized” malware. Such is the scale of the CIA’s undertaking that by 2016, its hackers had utilized more code than that used to run Facebook.
- The CIA had created, in effect, its “own NSA” with even less accountability and without publicly answering the question as to whether such a massive budgetary spend on duplicating the capacities of a rival agency could be justified.
- Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by rival states, cyber mafia and teenage hackers alike.
Also this scary possibility:
- As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks.
- The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations.
Journalist Michael Hastings, who in 2010 destroyed the career of General Stanley McChrystal and was hated by the military for it, was killed in 2013 in an inexplicably out-of-control car. This isn’t to suggest the CIA, specifically, caused his death. It’s to ask that, if these capabilities existed in 2013, what would prevent their use by elements of the military, which is, after all a death-delivery organization?
And lest you consider this last speculation just crazy talk, Richard Clarke (that Richard Clarke) agrees: “Richard Clarke, the counterterrorism chief under both Bill Clinton and George W. Bush, told the Huffington Post that Hastings’s crash looked consistent with a car cyber attack.'” Full and fascinating article here.
WiliLeaks Press Release
Here’s what WikiLeaks itself says about this first document cache (again, emphasis mine):
Press Release
Today, Tuesday 7 March 2017, WikiLeaks begins its new series of leaks on the U.S. Central Intelligence Agency. Code-named “Vault 7” by WikiLeaks, it is the largest ever publication of confidential documents on the agency.
The first full part of the series, “Year Zero”, comprises 8,761 documents and files from an isolated, high-security network situated inside the CIA’s Center for Cyber Intelligence in Langley, Virgina. It follows an introductory disclosure last month of CIA targeting French political parties and candidates in the lead up to the 2012 presidential election.
Recently, the CIA lost control of the majority of its hacking arsenal including malware, viruses, trojans, weaponized “zero day” exploits, malware remote control systems and associated documentation. This extraordinary collection, which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA. The archive appears to have been circulated among former U.S. government hackers and contractors in an unauthorized manner, one of whom has provided WikiLeaks with portions of the archive.
“Year Zero” introduces the scope and direction of the CIA’s global covert hacking program, its malware arsenal and dozens of “zero day” weaponized exploits against a wide range of U.S. and European company products, include Apple’s iPhone, Google’s Android and Microsoft’s Windows and even Samsung TVs, which are turned into covert microphones.
Since 2001 the CIA has gained political and budgetary preeminence over the U.S. National Security Agency (NSA). The CIA found itself building not just its now infamous drone fleet, but a very different type of covert, globe-spanning force — its own substantial fleet of hackers. The agency’s hacking division freed it from having to disclose its often controversial operations to the NSA (its primary bureaucratic rival) in order to draw on the NSA’s hacking capacities.
By the end of 2016, the CIA’s hacking division, which formally falls under the agency’s Center for Cyber Intelligence (CCI), had over 5000 registered users and had produced more than a thousand hacking systems, trojans, viruses, and other “weaponized” malware. Such is the scale of the CIA’s undertaking that by 2016, its hackers had utilized more code than that used to run Facebook. The CIA had created, in effect, its “own NSA” with even less accountability and without publicly answering the question as to whether such a massive budgetary spend on duplicating the capacities of a rival agency could be justified.
In a statement to WikiLeaks the source details policy questions that they say urgently need to be debated in public, including whether the CIA’s hacking capabilities exceed its mandated powers and the problem of public oversight of the agency. The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons.
Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by rival states, cyber mafia and teenage hackers alike.
Julian Assange, WikiLeaks editor stated that “There is an extreme proliferation risk in the development of cyber ‘weapons’. Comparisons can be drawn between the uncontrolled proliferation of such ‘weapons’, which results from the inability to contain them combined with their high market value, and the global arms trade. But the significance of “Year Zero” goes well beyond the choice between cyberwar and cyberpeace. The disclosure is also exceptional from a political, legal and forensic perspective.”
Wikileaks has carefully reviewed the “Year Zero” disclosure and published substantive CIA documentation while avoiding the distribution of ‘armed’ cyberweapons until a consensus emerges on the technical and political nature of the CIA’s program and how such ‘weapons’ should analyzed, disarmed and published.
Wikileaks has also decided to redact and anonymise some identifying information in “Year Zero” for in depth analysis. These redactions include ten of thousands of CIA targets and attack machines throughout Latin America, Europe and the United States. While we are aware of the imperfect results of any approach chosen, we remain committed to our publishing model and note that the quantity of published pages in “Vault 7” part one (“Year Zero”) already eclipses the total number of pages published over the first three years of the Edward Snowden NSA leaks.
Be sure to click through for the Analysis, Examples and FAQ sections as well.
“O brave new world,” someone once wrote. Indeed. Brave new world, that only the brave can live in.
____
1 Mind you, the leakers may have had a comprehensive enough view to be making an accurate call. But the real point is there are no actors who will be allowed to make an independent assessment.


That’s all I needed.
https://www.theguardian.com/us-news/2017/jan/10/fbi-chief-given-dossier-by-john-mccain-alleging-secret-trump-russia-contacts
Emphases mine. I had been sitting on this link trying to make sense of this part. Clearly, the Trump Whitehouse has some major leaks, which the MSM is exploiting. But the start of this article suggests that para-intelligence (is that a word? Eh, it is now) was the source of the allegedly damaging info.
This is no longer about the deep-state, but a rouge state, possibly guns for higher, each having fealty to specific political interests. The CIA arsenal wasn’t leaked. It was delivered.
hmm.. as far as I can see, noone seems to care here in Germany anymore about being spied on by our US friends, apart from a few alternative sources which are being accused of spreading fake news, of being anti-american, russian trolls, the matter is widely ignored
Privacy, what privacy?
As Snowden says “Saying you don’t care about privacy bcuz you’ve nothing to hide is like saying you don’t care about freedom of speech bcuz you have nothing to say.”
People, fight for our freedoms. PLEASE.
I have read a few articles about the Vault 7 leak that typically raise a few alarms I would like to comment on.
1) The fact that the
does not mean that it has broken encryption, just that it has a way to install a program at a lower level, close to the operating system, that will read messages before they are encrypted and sent by the messaging app, or just after they have been decrypted by it.
As a side note: banks have now largely introduced two-factor authentication when accessing online services. One enters username (or account number) and password; the bank site returns a code; the user must then enter this code into a smartphone app or a tiny specialized device, which computes and returns a value out of it; the user enters this last value into the entry form as a throw-away additional password, and gains access to the bank website.
I have always refused to use such methods on a smartphone and insist on getting the specialized “single-use password computer”, precisely because the smartphone platform can be subverted.
2) The fact that
is possible largely because smart TVs are designed by their manufacturers to serve as spying devices. “Weeping Angel” is not some kind of virus that turns normal devices into zombies, but a tool to take control of existing zombie devices.
The fact that smart TVs from Vizio, Samsung or LG constitute an outrageous intrusion into the privacy of their owners has been a known topic for years already.
3) The
is not a “scary possibility” either; various demonstrations of such feats on Tesla, Nissan, or Chrysler vehicles have been demonstrated in the past few years.
And the consequences have already been suggested (killing people by disabling their car controls on the highway for instance).
My take on this is that we should seriously look askance not just at the shenanigans of the CIA, but at the entire “innovative technology” that is imposed upon (computerized cars) or joyfully adopted by (smartphones) consumers. Of course, most NC readers are aware of the pitfalls already, but alas not the majority of the population.
4) Finally this:
Trump is arguably unfit for office, does not have a clue about many things (such as foreign relations), but by taxing him of being “erratic” Gaius Publius shows that he still does not “get” the Donald.
Trump has a completely different modus operandi than career politicians, formed by his experience as a real-estate mogul and media star. His world has been one where one makes outrageous offers to try anchoring the negotiation before reducing one’s claims — even significantly, or abruptly exiting just before an agreement to strike a deal with another party that has been lured to concessions through negotiations with the first one. NC once included a video of Trump doing an interactive A/B testing of his slogans during a campaign meeting; while changing one’s slogans on the spot might seem “erratic”, it is actually a very systematic market probing technique.
So stop asserting that Trump is “unpredictable” or “irrational”; this is underestimating him (a dangerous fault), as he is very consistent, though in an uncommon fashion amongst political pundits.
While I agree that it’s worth pointing out that the CIA has not broken any of the major encryption tools, even Snowden regards being able to circumvent them as worse, since people using encryption are presumably those who feel particularly at risk and will get a false sense of security and say things or keep data on their devices that they never never would if they thought they were insecure.
Re Gaius on Trump, I agree the lady doth protest too much. But I said repeatedly that Trump would not want to be President if he understood the job. It is not like being the CEO of a private company. Trump has vastly more control over his smaller terrain in his past life than he does as President.
And Trump is no longer campaigning. No more a/b testing.
The fact is that he still does not have effective control of the Executive branch. He has lots of open positions in the political appointee slots (largely due to not having even submitted candidates!) plus has rebellion in some organizations (like folks in the EPA storing data outside the agency to prevent its destruction).
You cannot pretend that Trump’s former MO is working at all well for him. And he isn’t showing an ability to adapt or learn (not surprising at his age). For instance, he should have figured out by now that DC is run by lawyers, yet his team has hardly any on it. This is continuing to be a source of major self inflicted wounds.
His erraticness may be keeping his opponents off base, but it is also keeping him from advancing any of his goals.
I believe we are in agreement.
Yes, not breaking encryption is devious, as it gives a false sense of security — this is precisely why I refuse to use those supposedly secure e-banking login apps on smartphones whose system software can be subverted, and prefer those non-connected, non-reprogrammable, special-purpose password generating devices.
As for Trump being incompetent for his job, and his skills in wheeling-dealing do not carrying over usefully to conducting high political offices, that much is clear. But he is not “erratic”, rather he is out of place and out of his depth.
I am writing this in the shower with a paper bag over my head and my iPhone in the microwave.
I have for years had a password-protected document on computer with all my important numbers and passwords. I have today deleted that document and reverted to a paper record.
Please tell readers more about the following for our benefit:
That is an example of the sort of thing I am talking about.
I think he means a machine dedicated to high-security operations like anything financial or bill-pay. Something that is not exposed to email or web-browsing operations that happen on a casual-use computer that can easily compromise. That’s not a bad way to go; it’s cheaper in terms of time than the labor-intensive approaches I use, but those are a hobby more than anything else. It depends on how much you have at stake if they get your bank account or brokerage service password.
I take a few basic security measures, which would not impress the IT crowd I hang out with elsewhere, but at least would not make me a laughingstock. I run Linux and use only open-source software; run ad-blockers and script blockers; confine risky operations, which means any non-corporate or non-mainstream website to a virtual machine that is reset after each use; use separate browsers with different cookie storage policies and different accounts for different purposes. I keep a well-maintained pfSense router with a proxy server and an intrusion detection system, allowing me to segregate my secure network, home servers, guest networks, audiovisual streaming and entertainment devices, and IoT devices each on their own VLANs with appropriate ACLs between them. No device on the more-secured network is allowed out to any port without permission, and similar rules are there for the IoT devices, and the VoIP tools.
The hardware to do all of that costs at least $700, but the real expense is in the time to learn the systems properly. Of course if you use Linux, you could save that on software in a year if you are too cheap to send a contribution to the developers.
It’s not perfect, because I still have computers turned on :) , but I feel a bit safer this way.
That said, absolutely nothing that I have here would last 30 milliseconds against anything the “hats” could use, if they wanted in. It would be over before it began. If I had anything to hide, really, I would have something to fear; so guess I’m OK.
open source software often has a lot of bugs to be exploioted. Wouldn’t it be easier to just do banking in person?
Banks discourage that by
a) charging extortionate fees for “in-person” operations at the counter;
b) closing subsidiaries, thus making it tedious and time-consuming to visit a branch to perform banking operations in person;
c) eliminating the possibility to perform some or even all usual operations in any other form than online (see the advent of “Internet only” banks).
In theoretical terms, all this is called “nudging”.
They’re key fobs handed to you by your IT dept. The code displayed changes every couple of minutes. The plus is there’s nothing sent over the air. The minus is the fobs are subject to theft, and are only good for connecting to ‘home’. And since they have a cost, and need to be physically handed to you, they’re not good fit for most two factor login applications (ie logging into your bank account).
see https://en.wikipedia.org/wiki/RSA_SecurID
I watched (fast forwarded through, really) Morning Joe yesterday to see what they would have to say about Wikileaks. The show mostly revolved around the health care bill and Trump’s lying and tweeting about Obama wiretapping him. They gave Tim Kaine plenty of time to discuss his recent trip to London talking to “some of our allies there” saying that they are concerned that “all the intelligence agencies” say the Rooskies “cyber hacked” our election, and since it looks like we aren’t doing anything when we are attacked, they KNOW we won’t do anything when they are attacked. (more red baiting)
The only two mentions I saw was about Wikileaks were, first, a question asked of David Cohen, ex Deputy Director of the CIA, who refused to confirm the Wikileaks were authentic, saying whatever tools and techniques the CIA had were used against foreign persons overseas, so there is no reason to worry that your TV is looking at you. And second, Senator Tom Cotton, who didn’t want to comment on the contents of Wikileaks, only saying that the CIA is a foreign intelligence service, collecting evidence on foreign targets to keep our country safe, and it does not do intelligence work domestically.
So that appears to be their story, the CIA doesn’t spy on us, and they are sticking with it, probably hoping the whole Wikileaks thing just cycles out of the news.
Thanks for mentioning Hastings. His death has always been more than suspicious.
Elite risk management reduction tool goes walkabout inverting its potential…..
disheveled…. love it when a plan comes together…..
The unwillingness of the main stream media (so far) to really cover the Wikileaks reveal is perhaps the bigger story. This should be ongoing front page stuff .. but it is not.
As for using ZeroHedge as a source for anything, can we give that a rest. That site has become a cesspool of insanity. It used to have some good stuff. Now it is just … unreadable. SAD
And yes… I know the hypocrisy of slamming ZH and the MSM at the same time … we live in interesting times.
Your remarks on ZH are an ad hominem attack and therefore a violation of site policies. The onus is on you to say what ZH got wrong and not engage in an ungrounded smear. The mainstream media often cites ZH.
NC more than just about any other finance site is loath to link to ZH precisely because it is off base or hyperventilating a not acceptably high percent of the time, and is generally wrong about the Fed (as in governance and how money works). We don’t want to encourage readers to see it as reliable. However, it is good on trader gossip and mining Bloomberg data.
And I read through its summary of the Wikileaks material as used by Gaius and there was nothing wrong with it. It was careful about attributing certain claims to Wikileaks as opposed to depicting them as true.
My rules for reading ZH:
1- Skip every article with no picture
2- Skip every article where the picture is a graph
3- Skip every article where the picture is of a single person’s face
4- Skip every afticle where the picture is a cartoon
5- Skip every article about gold, BitCoin, or high-frequency trading
6- Skip all the “Guest Posts”
7- ALWAYS click through to the source
8- NEVER read the comments
It is in my opinion a very high noise-to-signal source, but there is some there there.
Finding the TRUTH is NOT that easy.
Discerning a ‘news from noise’ is NEVER that easy b/c it is an art, developed by years of shifting through ever increasing ‘DATA information’ load. This again has to be filtered and tested against one’s own ‘critical’ thinking or reasoning! You have to give ZH, deserved credit, when they are right!
There is no longer a Black or white there, even at ZH! But it is one of the few, willing to challenge the main stream narrative ‘kool aid’
In addition to the “para-intelligence” community (hat tip Code named D) there are multiple enterprises with unique areas of expertise that interface closely with the CIA. The long-exposed operations, which include entrapment and blackmailing of key actors to guarantee complicity, “loyalty” and/or sealed lips, infect businesses, NGOs, law enforcement agencies, judges, politicians, and other government agencies. Equal opportunity employment for those with strong stomachs and a weak moral compass.
Yes I can’t remember where I read it but it was a tale passed around supposedly by an FBI guy that had, along with his colleagues, the job of vetting candidates for political office. They’d do their background research and pass on either a thick or thin folder full of all the compromising dirt on each potential appointee. Over time he said he was perturbed to notice a persistent pattern where the thickest folders were always the ones who got in.
Michael Hudson:
Sibel Edmonds, boiling frog, now newsbud.com. in relation to Dennis Hastert, judges and executive appointments were verified by FBI since the 1990s, the ones with the most skeletons in the closet were appointed.
https://www.youtube.com/watch?v=7XMoejT3lKs&feature=youtu.be&t=3m48s
http://www.newsbud.com/2015/09/20/dennis-hastert-case-clinton-scandals-fbi-the-1996-cointelpro-directive/
I find the notion that my consumer electronics may be CIA microphones somewhat irritating, but my imagination quickly runs off to far worse scenarios. (although the popular phase, “You’re tax dollars at work.” keeps running thru my head like a earworm. And whenever I hear “conservatives” speak of their desire for “small government”, usually when topics of health care, Medicare and social security come up, I can only manage a snort of incredulousness anymore)
One being malware penetrating our nuke power plants and shutting down the cooling system. Then the reactor slowly overheats over the next 3 days, goes critical, and blows the surrounding area to high heaven. We have plants all around the coast of the country and also around the Great Lakes Region – our largest fresh water store in a drought threatened future.
Then the same happening in our offensive nuke missile systems.
Some other inconvenient truths – the stuxnet virus has been redesigned. Kaspersky – premier anti malware software maker – had a variant on their corporate network for months before finally discovering it. What chance have we?
In China, hacking is becoming a consumer service industry. There are companies building high power data centers with a host of hacking tools. Anyone, including high school script kiddies, can rent time to use the sophisticated hacking tools, web search bots, and whatever, all hosted on powerful servers with high speed internet bandwidth.
Being a bit “spooked” by all this, I began to worry about my humble home computer and decided to research whatever products I could get to at least ward off annoying vandalism. Among other things, I did sign up for a VPN service. I’m looking at the control app for my VPN connection here and I see that with a simple checkbox mouse click I can make my IP address appear to be located in my choice of 40 some countries around the world. Romania is on the list!………………
“my consumer electronics may be CIA microphones…”
I haven’t tested this, so can’t confirm it works, but it sounds reasonable.
http://www.komando.com/tips/390304/secure-your-webcam-and-microphone-from-hackers
Actually, I very much doubt that does work. The mic “pickup” would feed its analog output to a DAC (digital to analog converter) which would convert the signal to digital. This then goes to something similar to a virtual com port in the operating system. Here is where a malware program would pick it up and either create a audio file to be sent to an internet address, or stream it directly there.
The article is just plugging in a microphone at the output jack. The malware got the data long before it goes thru another DAC and analog amp to get to the speakers or output jack.
s/b “plugging in a earbud at the output jack”. They’re confusing me too.
ah. thanks for vetting.
It’s actually a input/output jack or, if you will, a mic/headphone jack.
It depends on how it is hooked up internally. Old fashioned amateur radio headphones would disable the speakers when plugged in because the physical insertion of the plug pushed open the connection to the speakers. The jack that you plug the ear buds into might do the same, disconnecting the path between the built-in microphone and the ADC (actually it is an ADC not a DAC). The only way to know is to take it apart and see how it is connected.
The CIA is not allowed to operate in the US is also the panacea for the public. And some are buying it. Along with everyone knows they can do this is fueling the NOTHING to see here keep walking weak practically non existent coverage.
At what point do people quit negotiating in terrorism and errorism? For this is what the police, the very State itself has long been. Far beyond being illegitimate, illegal, immoral, this is a clear and ever present danger to not just it’s own people, but the rule of law itself. Blanket statements like we all know this… just makes the dangerously absurd normal… I’ll never understand that part of human nature. But hey, the TSA literally just keeps probing further each and every year. Bend over!
Trump may not be the one for the task but we the people desperately need people ‘unfit’, for it is the many fit who brought us to this point. His unfit nature is as refreshing on these matters in its chaotic honest disbelief as Snowden and Wiki revelations. Refreshing because it’s all we’ve got. One doesn’t have to like Trump to still see missed opportunity… so many should be telling him he could be the greatest pres ever if (for two examples) he fought tirelessly for single payer and to bring down this police state rather than the EPA or public education.
This cannot stand… on so many levels. Not only is the fourth amendment rendered utterly void, but even if it weren’t it falls far short of the protections we deserve.
No enemy could possibly be as bad as who we are and what we allow/do among ourselves. If an election can be hacked (not saying it was by Russia).. as these and other files prove anything can and will be hacked then our system is to blame, not someone else.
What amazes me is that the spooks haven’t manufactured proof needed to take Trump out of office… Bonfire of The Vanities style. I’d like to think the people have moved beyond the point they would believe manufactured evidence but the Russia thing proves otherwise.
These people foment world war while probing our every move and we do nothing!
If we wait for someone fit nothing will ever change… because we wait for the police/media/oligarch state to tell us who is fit.
…being “unfit” does not automatically make someone a savior.
But being fit by the standards of our ruling class, the “real owners” as Carlin called them is, in my book, an automatic proof that they are up to no good. Trump is not my cup of tea as a president but no one we have had in a while wasn’t clearly compromised by those who fund them. Did you ever wonder why we have never had a president or even a powerful member of congress that was not totally in the tank for that little country on the Eastern Mediterranean? Or the Gulf Monarchies? Do you think that is by accident? Do you think money isn’t involved? Talk about hacked elections! We should be so lucky as to have ONLY Russians attempting to affect our elections. Money is what hacks US elections and never forget that. To me it is laughable to discuss hacking the elections without discussing the real way our “democracy” is subverted–money not document leaks or voting machine hacks. It’s money.
Why isn’t Saudi Arabia on Trump’s list? Iran that has never been involved in a terrorist act on US soil is but not Saudi Arabia? How many 911 hijackers came from Iran? If anything saves Trump from destruction by the real owners of our democracy it is his devotion to the aforementioned countries.
The point again is not to remove him from office but to control him. With Trump’s past you better believe the surveillance state has more than enough to remove him from office. Notice the change in his rhetoric since inauguration? More and more he is towing the establishment Republican line. Of course this depends on whether you believe Trump is a break with the past or just the best liar out there. A very unpopular establishment would be clever in promoting their agent by pretending to be against him.
Anyone who still believes that the US is a democratic republic and not a mafia state needs to stick their heads deeper into the sands. When will the low information voters and police forces on whom a real revolution depends realize this is anyone’s guess. The day is getting closer especially for the younger generation. The meme among the masses is that government has always been corrupt and that this is nothing new. I do believe the level of immorality among the credentialed classes is indeed very new and has become the new normal. Generations of every man for himself capitalist philosophy undermining any sense of morality or community has finally done its work.
When people decry the “rule of law” I already know they really have never been in a courtroom. Spend a couple hours in foreclosure court. The rule of law hasn’t existed for a very long time in the good ol’ USA.
Go take a jaunt over to huffpo, at the time of this post there was not a single mention of vault 7 on the front page. Just a long series of anti trump administration articles.
Glad to know for sure who the true warmongers were all along.
We need another Church Commission.
No.. The Church commission was a sweep it under the rug operation. It got us FISA courts. More carte blanche secrecy, not less. The commission nor the rest of the system didn’t even hold violators of the time accountable.
We have files like Vault 7. Commissions rarely get in secret what we have right here before our eyes.
Well, how about a Truth and Reconciliation Commission?
Cute but the ANC lost the war by acceding to WTO entry (which “forbade” distributive politics, land/resource redistribution, nationalizations, etc.).
Need Langley surrounded and fired upon by tanks at this point.
Err on the side of caution.
River: Interesting historic parallel? I believe that the Ottomans got rid of the Janissaries that way, after the Janissaries had become a state within a state, by using cannons on their HQ
From Wiki entry, Janissaries:
The corps was abolished by Sultan Mahmud II in 1826 in the Auspicious Incident in which 6,000 or more were executed.[8]
“Nuke it from orbit … it’s the only way to be sure …. “
Took less than a minute to download the 513.33MB file. The passphrase is what JFK said he’d like to do to CIA: SplinterItIntoAThousandPiecesAndScatterItIntoTheWinds.
“The illegal we do immediately; the unconstitutional takes a little longer.” Henry Kissinger, 1975.
Here is Raimondo’s take:
Spygate
http://original.antiwar.com/justin/2017/03/07/spygate-americas-political-police-vs-donald-j-trump/
Perhapps overstated but well worth pondering.
Yeah I downloaded it the day it came out and spent an hour or so looking at it last night. First impressions – “heyyy this is like a Hackers Guide – the sort I used in the 80s, or DerEngel’s Cable Modem Hacking” of the 00s.
2nd impressions – wow it really gives foundational stuff – like “Enable Debug on PolarSSL”.
3rd impressions – “I could spend hours going thru this happily “.
4th impressions – I went looking for the “juicy bits” of interest to me – SOHO routers, small routers – sadly its just a table documenting routers sold around the world, and whether these guys have put the firmware in their Stash Repository. Original firmware, not hacked one. But the repository isn’t in the vault dump, AFAIK.
Its quite fascinating. But trying to find the “juicy stuff” is going to be tedious. One can spend hours and hours going thru it. To speed up going thru it, I’m going to need some tech sites to say “where to go”.
It seems clear that Wikileaks has not and will not release actual ongoing method “how-to” info or hacking scripts. They are releasing the “whats”, not the tech level detailed “hows”. This seems like a sane approach to releasing the data. The release appears to be for political discussion, not for spreading the hacking tools. So I wouldn’t look for “juicy bits” about detailed methodology. Just my guess.
That said, love what you’re doing digging into this stuff. I look forward to a more detailed report in future. Thanks.
Yves, I think that you much underestimate the extremity of these exposed violations of the security of freedom of expression, and of the security of private records. The WikiLeaks docs show that CIA has developed means to use all personal digital device microphones and cameras even when they are “off,” and to send all of your files and personal data to themselves, and to send your private messages to themselves before they are encrypted. They have installed these spyware in the released version of Windows 10, and can easily install them on all common systems and devices.
This goes far beyond the kind of snooping that required specialized devices installed near the target, which could be controlled by warrant process. There is no control over this extreme spying. It is totalitarianism now.
This is probably the most extreme violation of the rights of citizens by a government in all of history. It is far worse than the “turnkey tyranny” against which Snowden warned, on the interception of private messages. It is tyranny itself, the death of democracy.
Your first sentence is a bit difficult to understand. If you read Yves’ remarks introducing the post, she says that the revelations are “a big deal” “if the Wikileaks claim is even halfway true,” while coming down hard on the MSM and others for “pooh-pooh[ing]” the story. Did you want her to add more exclamation points?
So we have a zillion ways to spy and hack and deceive and assassinate, but no control. I think this is what the military refers to as “being overtaken by events.” It’s easy to gather information; not so easy to analyze it, and somehow impossible to act on it in good faith. With all this ability to know stuff and surveil people the big question is, Why does everything seem so beyond our ability to control it? We should know well in advance that banks will fail catastrophically; that we will indeed have sea level rise; that resources will run out; that water will be undrinkable; that people will be impossible to manipulate when panic hits – but what do we do? We play dirty tricks, spy on each other like voyeurs, and ignore the inevitable. Like the Stasi, we clearly know what happened, what is happening and what is going to happen. But we have no control.
My godfather was in the CIA in the late sixties and early seventies, and he said that outside of the President’s pet projects there was no way to sift through and bring important information to decision makers before it made the Washington Post (he is aware of the irony) and hit the President’s breakfast table.
Do you mean to say that the CIA leaked like a sieve? That’s my understanding of your post.
AS, I would interpret it as saying that there was so much coming in it was like trying to classify snowflakes in a snowstorm. They could pick a few subject areas to look at closely but the rest just went into the files.
Leaking like a sieve is also likely, but perhaps not the main point.
Not to worry, the new MATRIX ™ algo will sort it all out!
… The archive appears to have been circulated among government hackers and contractors in a authorized manner…
There, that looks the more likely framing considering CIA & DNI on behalf of the whole US IC seemingly fostered wide dissimination of these tools, information.
Demonstration of media control an added plus.
Cheers Yves
The Empire Strikes Back
WikiLeaks Has Joined the Trump Administration
Max Boot
Foreign Policy magazine
https://foreignpolicy.com/2017/03/08/wikileaks-has-joined-the-trump-administration/?utm_source=Sailthru&utm_medium=email&utm_campaign=New+Campaign&utm_term=%2AEditors+Picks
I guess we can only expect more of this.
Todd Pierce, on the other hand, nails it. (From his Facebook page.)
The East German Stasi could only dream of the sort of surveillance the NSA and CIA do now, with just as nefarious of purposes.
Perhaps the scare quotes around “international mobster” aren’t really necessary.
In all this talk about the various factions aligned with and against Trump, that’s one I haven’t heard brought up by anybody. With all the cement poured in Trump’s name over the years, it would be naive to think his businesses had not brushed up against organized crime at some point. Question is, whose side are they on?
Like all the other players, the “side” they are on is them-effing-selves. And isn’t that the whole problem with our misbegotten species, writ large?
Then there’s this: https://www.youtube.com/watch?v=s1Hzds9aGdA Maybe these people will be around and still eating after us urban insects and rodents are long gone? Or will our rulers decide no one should survive if they don’t?
To what extent do these hacks represent the CIA operating within the US? To what extent is that illegal? With the democrats worshipping the IC, will anyone in an official position dare to speak out?
Well we know chuckie won’t speak out..
http://thehill.com/homenews/administration/312605-schumer-trump-being-really-dumb-by-going-after-intelligence-community
FTA…”Schumer said that as he understands, intelligence officials are “very upset with how [Trump] has treated them and talked about them.””
I’ve long thought that the reason Snowden was pursued so passionately was that he exposed the biggest, most embarrassing secret: that the National “Security” Agency’s INTERNAL security was crap.
And here it is: “Wikileaks claims that the CIA lost control of the majority of its hacking arsenal ”
The CIA’s internal security is crap, too. Really a lot of people should be fired over that, as well as over Snowden’s release. We didn’t hear of it happening in the NSA, though I’m not sure we would have. Given Gaius’s description of Trump’s situation, it seems unlikely it will happen this time, either. One of my hopes for a Trump administration, as long as we’re stuck with it, was a thorough cleanout of the upper echelons in the IC. It’s obviously long overdue, and Obama wasn’t up to it. But I used the past tense because I don’t think it’s going to happen. Trump seems more interested in sucking up to them, presumably so they won’t kill him or his family. That being one of their options.
Ah, that’s the beauty of contracting it out. No one gets fired. Did anyone get fired because of Snowden? It was officially a contractor problem and since there are only a small number of contractors capable of doing the work, well you know. We can’t get new ones.
What I find by far the most distressing is this: “The CIA had created, in effect, its “own NSA” with even less accountability ….” [My emphasis]. It seems to characterize an organization that operates outside of any control and oversight – and one that is intentionally structuring itself that way. That worries me.
It is becoming increasingly clear that the Republic is lost because we didn’t stand gaurd for it. Blaming others don’t cut it either – we let it happen. And like the Germans about the Nazi atrocities, we will say that we didn’t know about it.
Hey, I didn’t let it happen. Stuff that spooks and sh!tes do behind the Lycra ™ curtain happens because it is, what is the big word again, “ineluctable.” Is my neighbor to blame for having his house half eaten by both kinds of termites, where the construction is such that the infestation and damage are invisible until the vast damage is done?
And just how were we supposed to stand guard against a secret and unaccountable organization that protected itself with a shield of lies? And every time some poor misfit complained about it they were told that they just didn’t know the facts. If they only knew what our IC knows they would not complain. It’s a dangerous world out there and only our brave IC can protect us from it. Come on. Stop blaming the victim and place the blame where it belongs–our IC and MIC. I say stop feeding the beast with your loyalty to a government that has ceased to be yours. Studiously avoid any military celebrations. Worship of the military is part of the problem. Remember, the people you thank for “their service” are as much victims as you are. Sadly they don’t realize that their service is to a rotten empire that is not worthy of their sacrifice but every time we perform the obligatory ritual of thankfulness we participate in the lie that the service is to a democratic country instead of an undemocratic empire. It’s clearly a case of Wilfred Owen’s classic “Dulce et Decorum Est”. Read the poem, google it and read it. It is instructive: ” you would not tell with such high zest To children ardent for some desperate glory, The old Lie: Dulce et decorum est Pro patria mori.” Make no mistake. It is a lie and it can only be undone if we all cease to tell it.
Here’s a pretty decent review of the various CIA programs revealed by Wikileaks:
http://www.libertyforjoe.com/2017/03/what-is-vault-7.html
“These CIA revelations in conjunction with those of the NSA paints a pretty dark future for privacy and freedom. Edward Snowden made us aware of the NSA’s program XKEYSCORE and PRISM which are utilized to monitor and bulk collect information from virtually any electronic device on the planet and put it into a searchable database. Now Wikileaks has published what appears to be additional Big Brother techniques used by a competing agency. Say what you want about the method of discovery, but Pandora’s box has been opened.”
Thanks for linking to my article. I appreciate it.
re: “As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks.”
Gary Webb also believed his car was being tampered with right before his alleged suicide.